pem文件怎么用
1、说明:a)首先使用BASE64解码,如果是非ANSI TXT格式,需要做转换。b)一个RSA私钥包含一下信息(1024位):
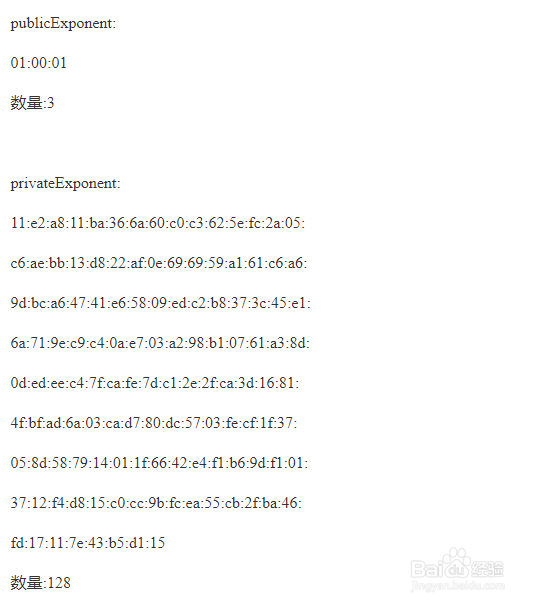
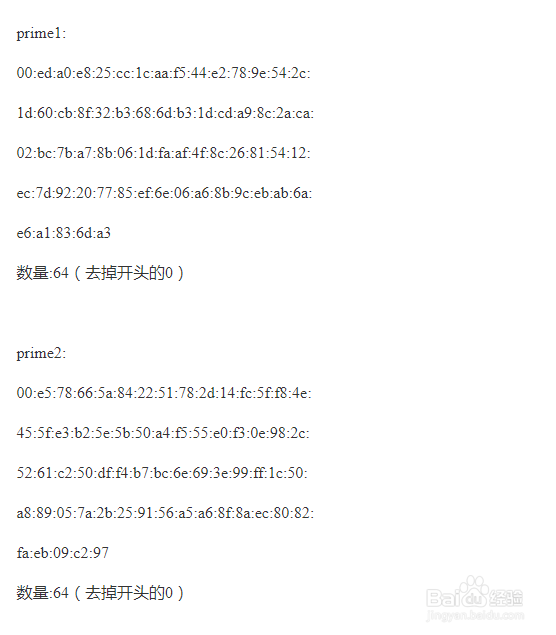
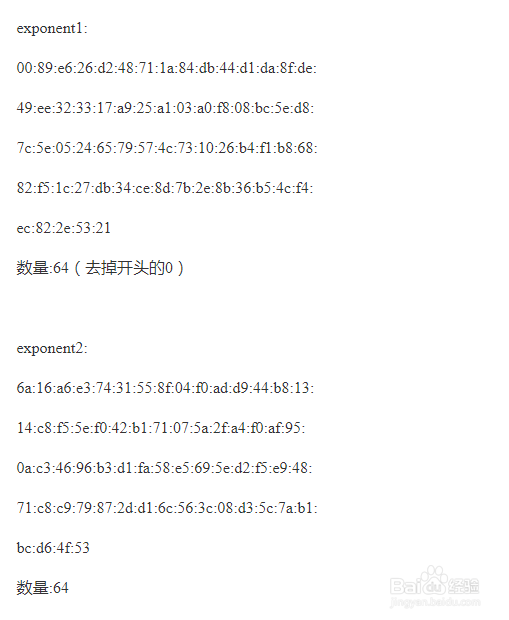
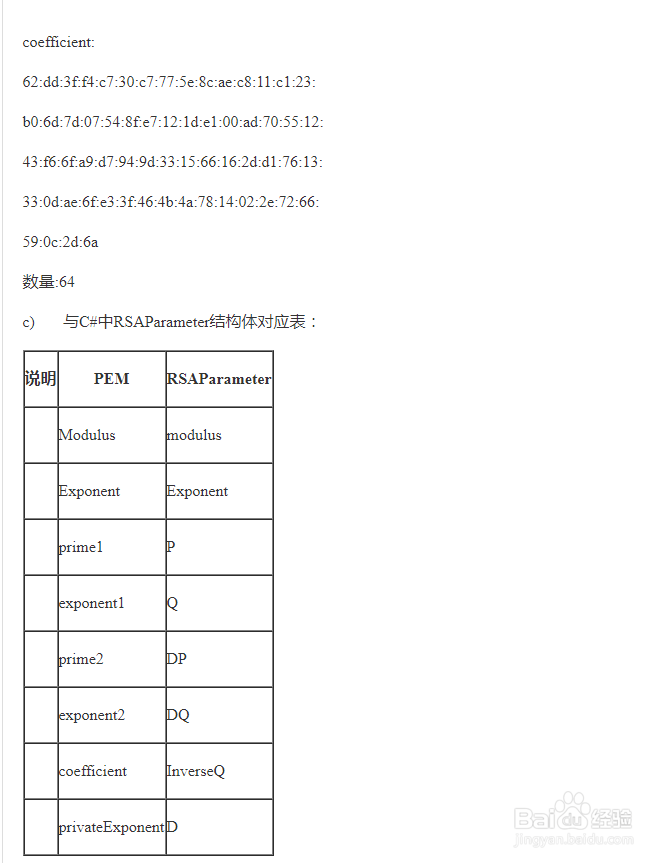
2、ssl rsa -in key.pem 颍骈城茇-noout -textmodulus:00:d5:00:b2:18:c3:04:d1:ac:80:c6:22:a0:cc:5c:f1:c0:4a:83:95:e5:c9:88:ae:31:64:ab:e1:15:42:de:1a:da:bc:f5:d2:05:05:74:9d:d3:86:94:9b:9d:74:bb:e5:72:a4:b8:40:27:61:88:d4:ac:20:b0:2b:1c:1e:d7:9b:43:c5:06:b6:3a:b4:42:f0:5a:22:38:23:74:99:4a:50:f1:f1:54:11:5a:44:0b:40:cf:83:8a:73:6c:34:15:98:0a:7d:cf:0e:e5:00:8d:07:40:f7:7d:fb:3f:64:35:1b:5d:a3:40:a9:51:fa:92:7d:34:ef:03:fe:e0:59:56:31:25数量:128publicExponent:01:00:01数量:3privateExponent:11:e2:a8:11:ba:36:6a:60:c0:c3:62:5e:fc:2a:05:c6:ae:bb:13:d8:22:af:0e:69:69:59:a1:61:c6:a6:9d:bc:a6:47:41:e6:58:09:ed:c2:b8:37:3c:45:e1:6a:71:9e:c9:c4:0a:e7:03:a2:98:b1:07:61:a3:8d:0d:ed:ee:c4:7f:ca:fe:7d:c1:2e:2f:ca:3d:16:81:4f:bf:ad:6a:03:ca:d7:80:dc:57:03:fe:cf:1f:37:05:8d:58:79:14:01:1f:66:42:e4:f1:b6:9d:f1:01:37:12:f4:d8:15:c0:cc:9b:fc:ea:55:cb:2f:ba:46:fd:17:11:7e:43:b5:d1:15数量:128prime1:00:ed:a0:e8:25:cc:1c:aa:f5:44:e2:78:9e:54:2c:1d:60:cb:8f:32:b3:68:6d:b3:1d:cd:a9:8c:2a:ca:02:bc:7b:a7:8b:06:1d:fa:af:4f:8c:26:81:54:12:ec:7d:92:20:77:85:ef:6e:06:a6:8b:9c:eb:ab:6a:e6:a1:83:6d:a3数量:64(去掉开头的0)prime2:00:e5:78:66:5a:84:22:51:78:2d:14:fc:5f:f8:4e:45:5f:e3:b2:5e:5b:50:a4:f5:55:e0:f3:0e:98:2c:52:61:c2:50:df:f4:b7:bc:6e:69:3e:99:ff:1c:50:a8:89:05:7a:2b:25:91:56:a5:a6:8f:8a:ec:80:82:fa:eb:09:c2:97数量:64(去掉开头的0)exponent1:00:89:e6:26:d2:48:71:1a:84:db:44:d1:da:8f:de:49:ee:32:33:17:a9:25:a1:03:a0:f8:08:bc:5e:d8:7c:5e:05:24:65:79:57:4c:73:10:26:b4:f1:b8:68:82:f5:1c:27:db:34:ce:8d:7b:2e:8b:36:b5:4c:f4:ec:82:2e:53:21数量:64(去掉开头的0)exponent2:6a:16:a6:e3:74:31:55:8f:04:f0:ad:d9:44:b8:13:14:c8:f5:5e:f0:42:b1:71:07:5a:2f:a4:f0:af:95:0a:c3:46:96:b3:d1:fa:58:e5:69:5e:d2:f5:e9:48:71:c8:c9:79:87:2d:d1:6c:56:3c:08:d3:5c:7a:b1:bc:d6:4f:53数量:64coefficient:62:dd:3f:f4:c7:30:c7:77:5e:8c:ae:c8:11:c1:23:b0:6d:7d:07:54:8f:e7:12:1d:e1:00:ad:70:55:12:43:f6:6f:a9:d7:94:9d:33:15:66:16:2d:d1:76:13:33:0d:ae:6f:e3:3f:46:4b:4a:78:14:02:2e:72:66:59:0c:2d:6a数量:64
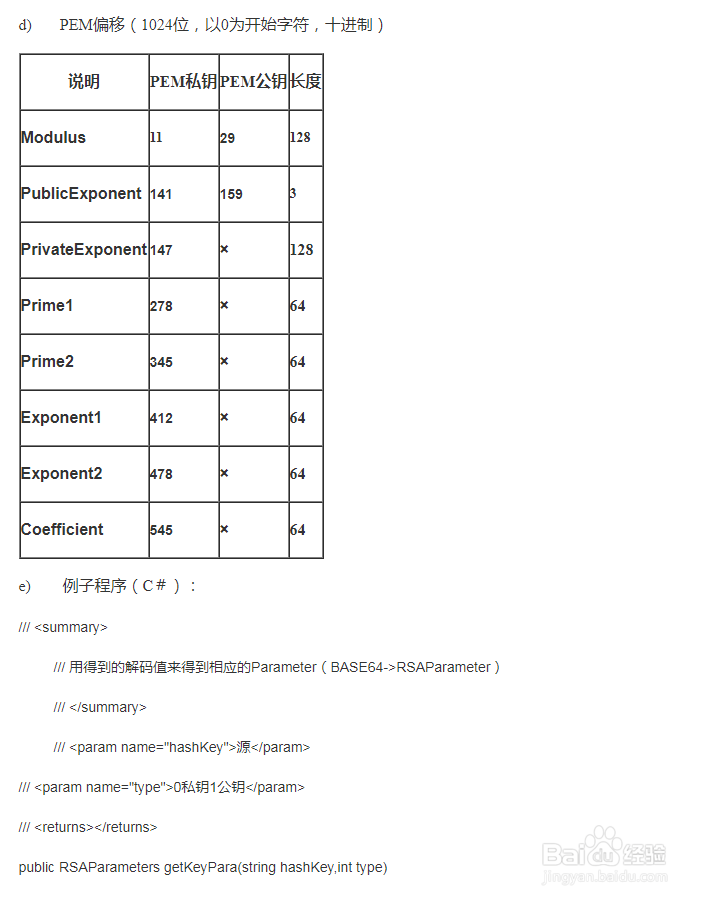
3、>openc)与C#中RSAParameter结构体对应表:说明PEMRSAParameterModulusmodulusExponentExponentprime1Pexponent1Qprime2DPexponent2DQcoefficientInverseQprivateExponentDd)PEM偏移(1024位,以0为开始字符,十进制)说明PEM私钥PEM公钥长度Modulus1129128PublicExponent1411593PrivateExponent147×128Prime1278×64Prime2345×64Exponent1412×64Exponent2478×64Coefficient545×64
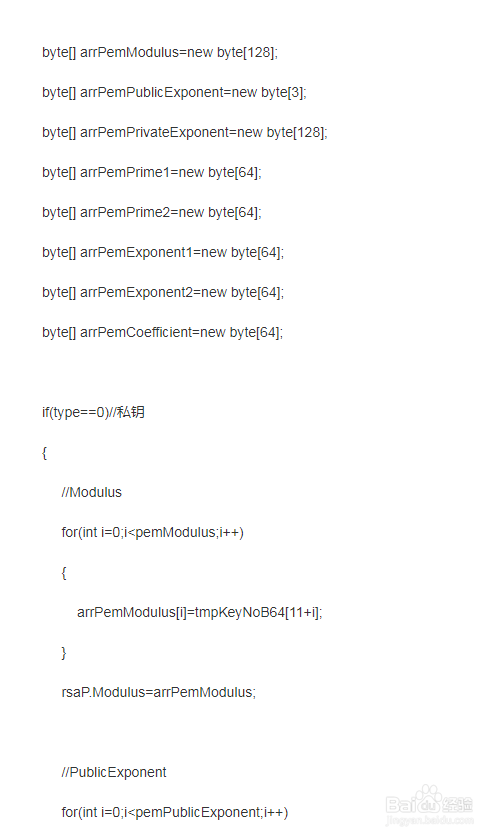
4、e)例子程序(C#):///<summary>///用得到的解码值来得到相应的Parameter(BASE64->RSAParameter)///</summary>///<param name="hashKey">源</param>///<param name="type">0私钥1公钥</param>///<returns></returns>publicRSAParameters getKeyPara(stringhashKey,inttype){RSAParameters rsaP=newRSAParameters();byte[] tmpKeyNoB64=Convert.FromBase64String(hashKey);intpemModulus=128;intpemPublicExponent=3;intpemPrivateExponent=128;intpemPrime1=64;intpemPrime2=64;intpemExponent1=64;intpemExponent2=64;intpemCoefficient=64;
5、byte[] arrPemModulus=newbyte[128];byte[] arrPemPublicE旌忭檀挢xponent=newbyte[3];byte[] arrPemPrivateExponent=newbyte[128];byte[] arrPemPrime1=newbyte[64];byte[] arrPemPrime2=newbyte[64];byte[] arrPemExponent1=newbyte[64];byte[] arrPemExponent2=newbyte[64];byte[] arrPemCoefficient=newbyte[64];if(type==0)//私钥{//Modulusfor(inti=0;i<pemModulus;i++){arrPemModulus[i]=tmpKeyNoB64[11+i];}rsaP.Modulus=arrPemModulus;//PublicExponentfor(inti=0;i<pemPublicExponent;i++){arrPemPublicExponent[i]=tmpKeyNoB64[141+i];}rsaP.Exponent=arrPemPublicExponent;//PrivateExponentfor(inti=0;i<pemPrivateExponent;i++){arrPemPrivateExponent[i]=tmpKeyNoB64[147+i];}rsaP.D=arrPemPrivateExponent;//Prime1for(inti=0;i<pemPrime1;i++){arrPemPrime1[i]=tmpKeyNoB64[278+i];}rsaP.P=arrPemPrime1;//Prime2for(inti=0;i<pemPrime2;i++){arrPemPrime2[i]=tmpKeyNoB64[345+i];}rsaP.Q=arrPemPrime2;
6、//Exponent1for(inti=0;i<pemExponent1;i++){arrPemExponent1[i]=tmpKeyNoB64[412+i];}rsaP.DP=arrPemExponent1;//Exponent2for(inti=0;i<pemExponent2;i++){arrPemExponent2[i]=tmpKeyNoB64[478+i];}rsaP.DQ=arrPemExponent2;//Coefficientfor(inti=0;i<pemCoefficient;i++){arrPemCoefficient[i]=tmpKeyNoB64[545+i];}rsaP.InverseQ=arrPemCoefficient;}else//公钥{for(inti=0;i<pemModulus;i++){arrPemModulus[i]=tmpKeyNoB64[29+i];}rsaP.Modulus=arrPemModulus;for(inti=0;i<pemPublicExponent;i++){arrPemPublicExponent[i]=tmpKeyNoB64[159+i];}rsaP.Exponent=arrPemPublicExponent;}returnrsaP;}